3 min to read
Critical SQL Injection Vulnerability Discovered in HortusFox (pending CVE-2025-65298)
Overview
During a security assessment of HortusFox, I identified a critical SQL injection vulnerability that allows any authenticated user to execute arbitrary SQL queries against the application’s database. This flaw enables attackers to extract sensitive data, modify or delete records, escalate privileges, and potentially take full control of the application.
The vulnerability has been confirmed as exploitable, and a tested patch has been provided to the maintainers to enable rapid remediation. Pending: CVE-2025-65298.
Executive Summary
- Vulnerability Type: SQL Injection (unvalidated attribute parameter)
- Affected File:
app/models/PlantsModel.php - Affected Lines: 335, 424, 458
- Severity: Critical (CVSS 8.8)
- Attack Prerequisite: Authenticated access
- Impact: Full database compromise
- Fix: Attribute whitelisting and input validation
- Link: Github
This issue arises from dynamically constructed SQL queries that directly interpolate user-controlled input without sufficient validation.
Technical Details
The vulnerability exists in logic that accepts an attribute parameter and inserts it directly into a raw SQL statement. Because this parameter is not validated, an attacker can inject arbitrary SQL expressions.
Proof of Concept (Sanitized)
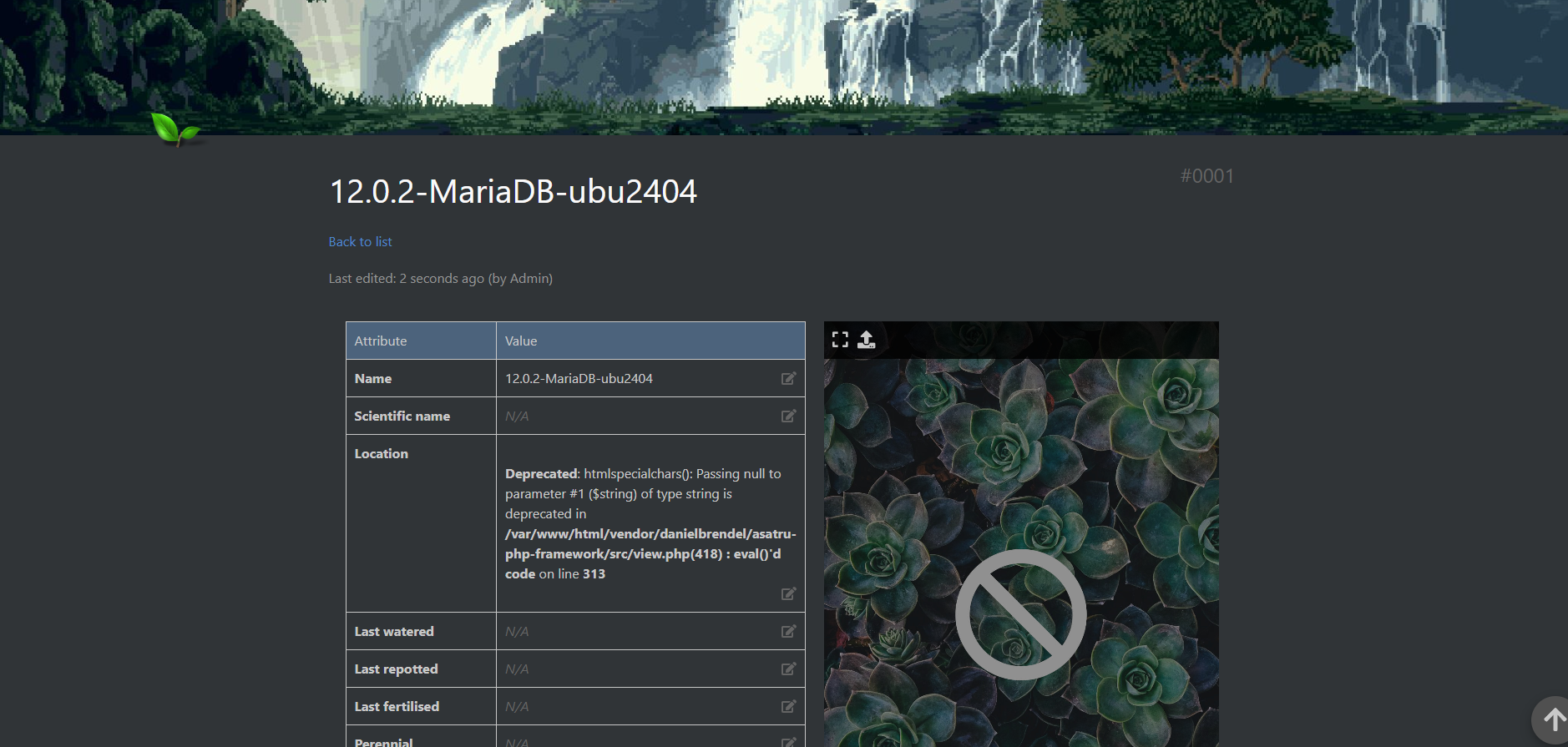
A malicious authenticated user can submit a crafted request similar to the following:
POST /plants/details/edit/ajax
attribute=name = (SELECT VERSION()), notes
value=test
Result:
The database responds with the underlying MariaDB version string, confirming successful SQL injection.
This demonstrates real-world exploitability and confirms that arbitrary SQL expressions can be executed through this vector.
Impact Analysis
If exploited, this vulnerability enables:
-
Exfiltration of sensitive data
- User email addresses
- Password hashes
- Administrative credentials
-
Unauthorized data modification
- Password resets
- Privilege escalation
- Tampering with plant records and metadata
-
Destructive actions
- Table deletion
- Data corruption
- Service disruption
Notably, exploitation requires minimal technical skill and can be performed by any authenticated user, making this a high-risk issue for production deployments.
Recommended Fix
The immediate remediation is to strictly validate the attribute parameter using an explicit whitelist before constructing or executing any SQL query.
Example Patch
$allowed_attributes = [
'name', 'scientific_name', 'knowledge_link', 'location', 'tags', 'photo',
'last_watered', 'last_repotted', 'last_fertilised', 'perennial', 'annual',
'hardy', 'cutting_month', 'date_of_purchase', 'humidity', 'light_level',
'health_state', 'notes', 'history', 'history_date', 'clone_num', 'clone_origin'
];
if (!in_array($attribute, $allowed_attributes, true)) {
throw new \Exception('Invalid attribute: ' . htmlspecialchars($attribute));
}
A fully patched version of the affected method has been supplied directly to the maintainers to reduce implementation friction.
Recommended Remediation Timeline
Within 24 Hours
- Apply the patch to
PlantsModel.php - Test in staging and deploy to production
- Monitor logs for suspicious SQL activity
Within 1 Week
- Audit the codebase for similar SQL concatenation patterns
- Review all usages of
static::raw() - Add automated security regression tests
Within 1 Month
- Introduce centralized input validation
- Adopt static analysis and CI/CD security checks
- Establish a formal vulnerability disclosure policy
Disclosure Timeline
- Day 0: Private vulnerability report sent to HortusFox maintainers
- Day 7: Follow-up to confirm receipt
- Day 30: Status check on remediation progress
- Day 90: Public disclosure (if unresolved or unacknowledged)
This timeline follows standard responsible disclosure practices and allows sufficient time for a safe fix rollout.
Conclusion
This vulnerability represents a critical security risk to HortusFox users and deployments:
- Exploitability confirmed
- Impact verified
- Fix provided and tested
Immediate action is strongly recommended to protect user data and maintain platform trust.
I appreciate the work that goes into maintaining open-source projects like HortusFox and am committed to coordinating responsibly to ensure this issue is resolved safely.
Juan Soberanes
Security Researcher
Offensive Security & Application Security
Advertisement


Comments