4 min to read
CVE-2025-64115: Unvalidated Referer Redirect & SSRF in Movary

Author: Juan Soberanes (CyberDucky)
Date: 2025-10-30
Severity: High (CVSS 8.1)
CVE: CVE-2025-64115
GitHub Advisory: GHSA-pm58-79jw-q79f
References:
Overview
While reviewing the Movary codebase, I discovered a high-severity vulnerability caused by unvalidated use of the HTTP_REFERER header for redirects. This design flaw allowed attackers to abuse application redirect behavior, enabling both open redirect phishing campaigns and potential Server-Side Request Forgery (SSRF) attacks.
This issue was responsibly disclosed to the maintainers and has since been remediated.
Vulnerability Summary
- Vulnerability Type: Unvalidated Referer Header Redirect / SSRF
- Severity: High (CVSS 8.1)
- Affected Versions:
<= 0.68.0 - Patched Version:
0.69.0 - Location:
src/HttpController/Web/SettingsController.php
Impact
Successful exploitation could allow for:
- Mass-scale phishing campaigns
- Credential harvesting via open redirects
- Server-Side Request Forgery against internal infrastructure
- Targeting of cloud metadata endpoints (AWS, GCP, Azure)
- Service reconnaissance and data exfiltration
Vulnerable Endpoints
The following endpoints were found to perform redirects directly from the untrusted HTTP_REFERER header:
/settings/account/delete-history
/settings/account/delete-ratings
/settings/account/delete-account
Root Cause
The application trusted and used the value of:
$_SERVER['HTTP_REFERER']
as a redirect URL without verifying that the destination belonged to the same origin.
Because Referer is a client-controlled request header, attackers could fully manipulate its value.
Example Attack
Open Redirect Phishing
- The attacker hosts a malicious webpage.
- The victim clicks a link leading to Movary from that page.
- The browser sends the attacker’s domain as the
Refererheader. - Movary processes a request to one of the vulnerable endpoints.
- Movary redirects the victim right back to the attacker’s phishing page.
Once redirected, victims may be prompted to:
- Re-enter login credentials
- Approve fake account changes
- Download malware
SSRF Abuse
Using crafted redirection flows, an attacker could coercively route server requests toward:
- Internal services not intended for public exposure
-
Cloud provider metadata services such as:
http://169.254.169.254(AWS)- GCP and Azure equivalents
Scalability
This exploitation pattern requires:
- Minimal technical complexity
- Only a low-cost domain
- No authentication bypass
- No elevated privileges
The ease of exploitation enables large-scale abuse and automation.
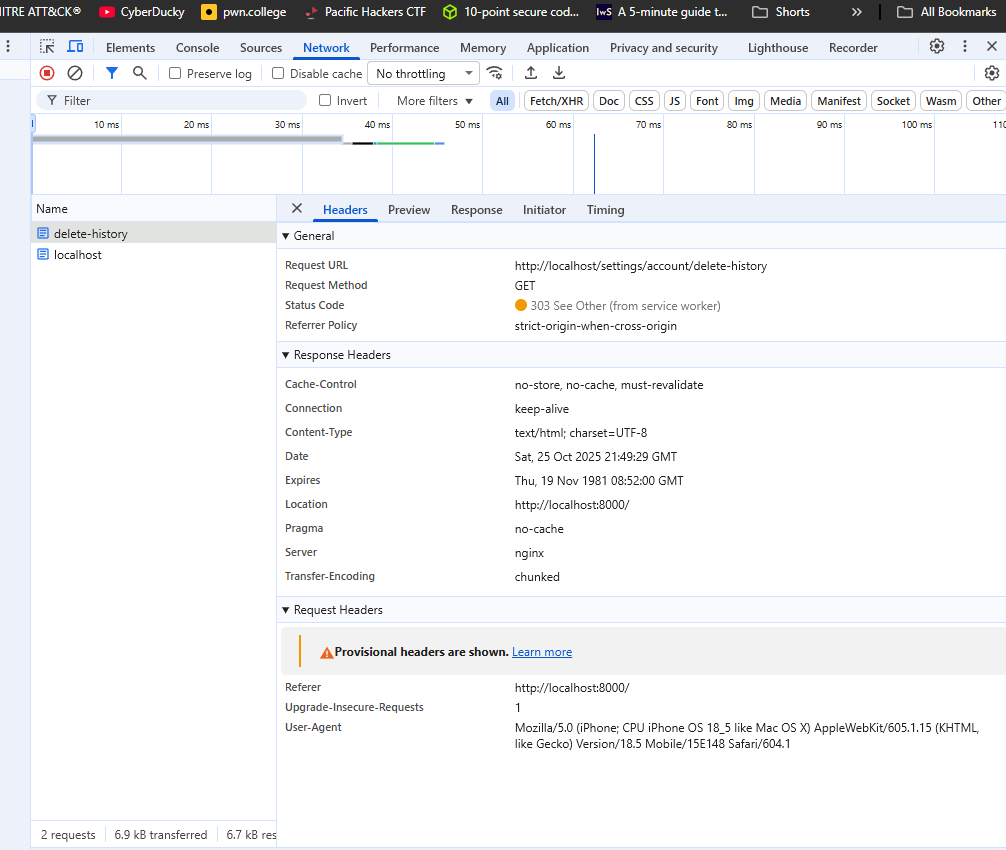
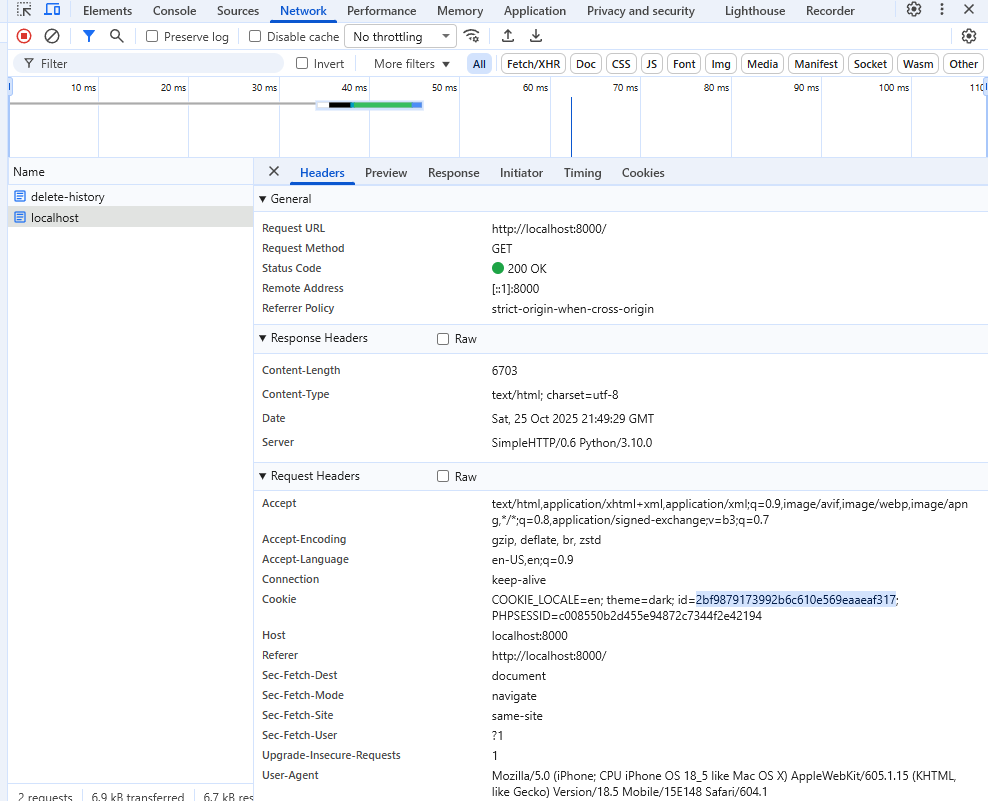
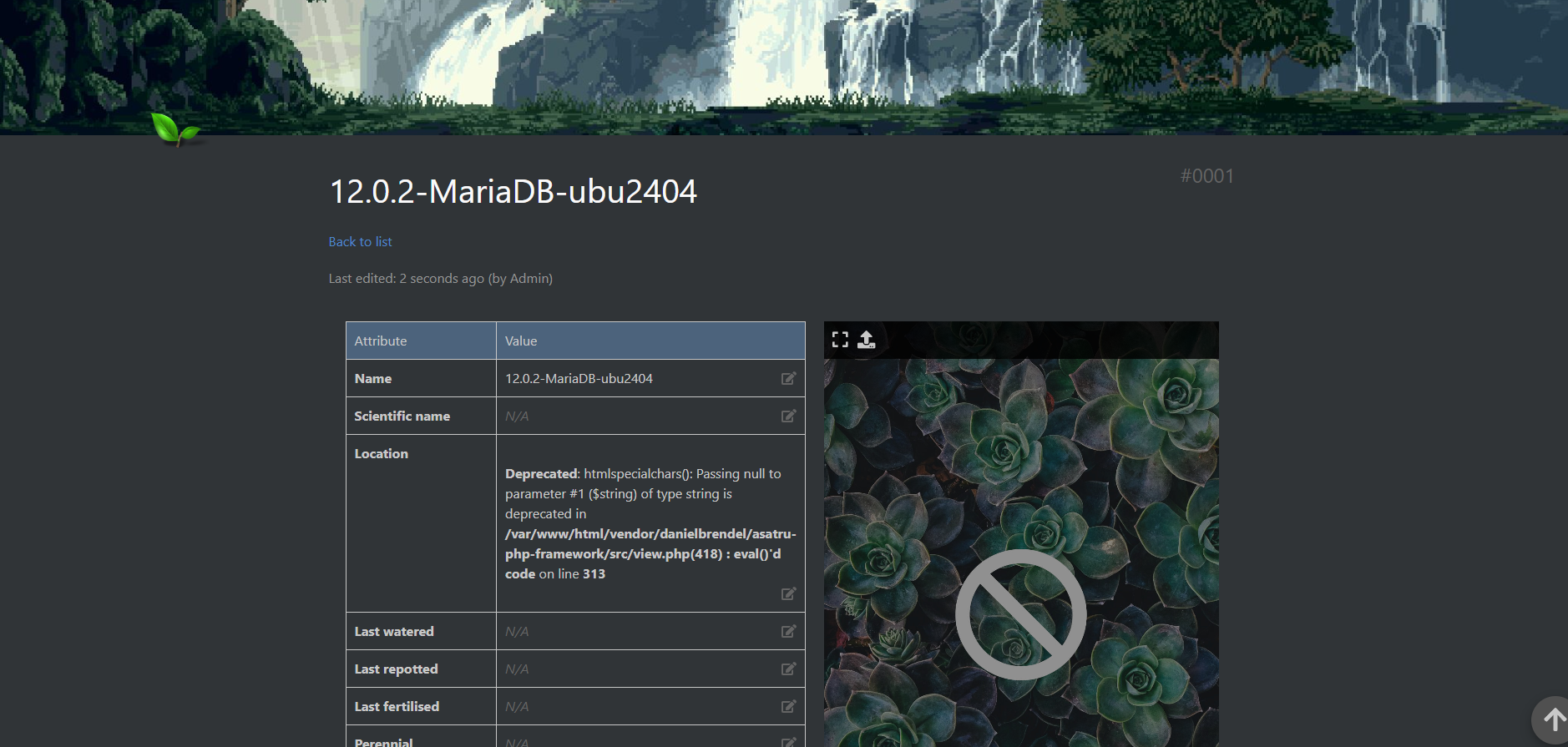
Proof of Concept
The vulnerability was verified via live tests in a controlled local environment. Demonstrations included:
- Malicious referer manipulation
- Redirect chaining to attacker-controlled pages
- SSRF probe redirections
Full exploitation workflows were documented in the private disclosure reports.
Recommended Remediations
Immediate Fix — Validate Referer Redirects
Only allow redirects to locations that remain within the application’s origin.
private function getSafeRedirectUrl(): string
{
$referer = $_SERVER['HTTP_REFERER'] ?? '';
if (empty($referer)) {
return '/settings';
}
$refererParts = parse_url($referer);
$currentHost = $_SERVER['HTTP_HOST'];
// Only allow same-origin redirects
if (isset($refererParts['host']) && $refererParts['host'] === $currentHost) {
return $referer;
}
return '/settings';
}
Defense-in-Depth Recommendations
To further reduce attack surface:
- Add CSRF protection tokens to all destructive endpoints
- Replace state-changing
GETrequests with POST or DELETE - Implement rate limiting on sensitive routes
- Avoid trusting any client-controlled header for application control flow
Maintainer Fixes
Movary deployed two major fixes.
1. Global Referer Validation Middleware
- Introduced middleware to validate
HTTP_REFERERagainstHTTP_HOSTfor all sensitive routes -
Mismatched hosts now:
- Block requests
- Return errors
- Generate warning logs
Reference: Issue #713
2. HTTP Method Refactor
-
Updated account data destruction endpoints:
- From:
GET - To:
DELETE
- From:
This prevents:
- CSRF chaining via hyperlink attacks
- Accidental account deletion through link previews or crawlers
Reference: Issue #717
Disclosure Timeline
| Date | Event |
|---|---|
| 2025-10-25 | Vulnerability discovered and validated in local environment |
| 2025-10-30 | Initial responsible disclosure submitted |
| Following weeks | Maintainer remediation and validation |
| After patch release | Coordinated public disclosure |
Testing Environment
- Application Version: Latest
mainbranch as of 2025-10-25 - Environment: Local development instance only
- Production Testing: None — no live systems were accessed or impacted``
Credits
Discovery & Disclosure
Juan Soberanes — CyberDucky
GitHub: @cyberducky0o0
Final Notes
This vulnerability demonstrates a common but dangerous assumption:
Never trust HTTP headers as authoritative input.
Even fields that appear benign, such as Referer, can become powerful attack vectors when they influence application routing or redirection flows.
Proper validation and safer HTTP method usage are mandatory for preventing this class of attack.
🦆 CyberDucky Security Research Teaching exploitation, defense, and vulnerability research — one bug at a time.
Advertisement

Comments